The basic building block of a modern block cipher is the substitution box (S-box), which provides the nonlinearity that is required when fending off advanced cryptanalytic methods. The novel approach introduced in the present work is computationally efficient, but it is still a robust algorithm for generating an 8 8 S-box through an operation of a specifically defined bijective mapping over the Galois Field \(GF(2^{8})\). The proposed S-box was strictly tested on a broad range of standard security criteria to prove its cryptographic integrity. A good performance has been identified in the analysis with a nonlinearity of 112 and linear approximation probability (LAP) of 0.0625, and the outstanding element of differential approximation probability (DAP) of 0.0156. Using a strong cryptographic construction, the new AES structure implements an S-box whose avalanche-like properties are best shown by a low value of the strict avalanche criterion (SAC) 0.4995 and strong bit independence (BIC) scores. The experimental results have supported the hypothesis that the proposed S-box has a much greater resistance to both the differential and the linear attacks compared with the state-of-the-art algebraic, heuristic, and chaos-based designs. In order to show how applicable the S-box can be in practical terms, a framework of image encryption incorporates the use of the S-box in it, whereby it operates as the basis element of a block cipher. The resulting cipher image achieved an entropy of 7.9978, which demonstrates a very high degree of randomness and strong resistance to statistical attacks. The feature article introduces a significant step towards systematizing cryptographic design through the introduction of a sound and carefully defined framework for the construction of high-security S-boxes.
Cryptography is used to make communication secure when there is a third party. Communication and information security (CIS) refers to the planned use of scientific principles and feasible methods aimed at protecting communication and information against unauthorized penetration or usage. Working on plain-text data, the field makes use of collections of mathematical algorithms and protocols to produce and process coded messages that are inaccessible to any other party besides the intended recipient. The cryptographic methods, especially the application of codes and ciphers, are an ancient tradition, the historical value of which is rather significant and complex. The historical sources show that encrypted messages have been used by humans for at least five millennia since the Indus Valley writing, as well as the Egyptian hieratic and Demotic writing systems. An early version of the substitution cipher emerged in Mesopotamian writings in the ancient Near East, and advanced cryptography processes emerged in the classical world of Ancient Greece and Ancient Rome, some of which have not yet been cracked. Throughout this wide span of technology, one can find a striking uniformity in cryptographic procedure, often conforming to one or more shared sets of functional and structural principles. The most common scholarly view as of recent times is that cryptography developed along with writing itself and that a developing understanding of how to improve the script led to improved methods of systematic encryption. These developments were incubated throughout the early writing systems; e.g., the cuneiform writing and the Egyptian hieroglyphics allowed semiotic units to be abstracted and used to hide. It was also the modular nature of scripts that promoted such work, which was the backbone of coming up with cryptography keys by cataloguing the correspondences. In the modern period, cryptographic research has been reimagined as a scrupulously computational practice, and its foundation is discrete mathematics. The terminology has also changed to reflect the field-specific use of terms, and the term cipher now refers to any such encryption scheme where the inner workings are deterministic. Regarding nominal typologies, modern cryptographers distinguish between symmetric and asymmetric systems, with symmetric systems using only a single key to both encrypt and decrypt, and the asymmetric ones having different keys for different processes.
In this article, symmetric cryptography or secret key cryptography is used for data encryption. In this type of encryption, the same key is used for both encrypting and decrypting data. In other words, both the sender and recipient use the same key to scramble and unscramble the information. There are several types of symmetric key algorithms to encrypt and decrypt data. The most popular ones include Data Encryption Standard (DES), Triple DES (3DES), Advanced Encryption Standard (AES), Blowfish, Twofish, and RC4. One of the main challenges with this cryptography is securely distributing the key to the sender and receiver. Once the key used to transmit a message is intercepted, the attacker will easily decipher the message. These vulnerabilities are possible to overcome by applying safe key-exchange arrangements, including key consent procedures and electronic attestations. Due to their effective nature, they are much more reliable on a large scale, like in industry applications. The protection of sensitive information with the help of Advanced Encryption Standard (AES) offers an advanced level of security. Symmetric key cryptography is an essential part of today’s security systems as it has a broad range of applications such as encryption of digital data, password protection systems, and digital rights management plans. Stream ciphers and block ciphers are the two main classes of symmetric-key cryptography. Block ciphers include systems with fixed-length blocks of data, and each block gets a unique key applied to it. In contrast, stream ciphers operate on one bit or one byte, modifying it by using a key stream derived from the underlying secret key. Two of the main components of block ciphers are the S-box and P-box. S-boxes perform as the cryptography primitives that add a non-linear relation into the process of encryption, and make it harder for the adversary to retrieve the plain text based on the cipher text. They help to achieve resistance against statistical attacks and provide a high degree of diffusion in the cipher. The P-box resides at the current center stage of symmetric-key block cipher design, due to its ability to cause diffusion of input data by spreading the effect of a particular input bit to a number of output bits. This helps in achieving a high degree of confusion and ensures that changes in any input bits affect a large number of output bits. The design structure and performance characteristics of both substitution S-boxes and permutation P-boxes behave very differently in different ciphers. Such components are designed very carefully by cryptographers to ensure that the encryption scheme constructs them to ensure that their security and resistance are sound.
A S-box is a core component of symmetric-key block ciphers since it gives these vital properties of non-linearity, confusion, and diffusion to the whole encryption and decryption process. In cryptographic texts, an S-box is supposed to resist both linear and differential cryptanalysis. Its development, therefore, has to combine various mathematical structures, and in this case, it involves intersections of Boolean algebra, symmetric groups, Galois fields, and Galois rings. The careful design and sturdiness of an S-box have a strong impact on the cryptographic strength of a block cipher as a whole. Accuracy and proper testing of elements such as an S-Box to achieve overall security and robustness of block cipher algorithms is necessary. Currently, AES [1] is a popular algorithm of symmetric-key cryptography, and is designed by J. Daemen and V. Rijmen. Modern cryptography deals with complicated S-box generation practices, with the development of more secure practices remaining a long-standing enthusiasm. M. T. Tran, D. K. Bui, and A. D. Duong developed another S-Box [2] using binary gray transformation on the AES S-Box. Two scientists, Cui L. Cao Y., made an S-Box [3] and named it APA S-box, and increased the algebraic complexity of AES. In [4] I. Hussain, T. Shah, H. Mahmood, and M.A. Gondal devised another algorithm for substitution boxes based on PGL groups. [5] introduced a proficient image encryption algorithm that leverages chaos and multiple S-boxes, showcasing high efficiency. In [6], a new algorithm for the construction of secure keys for AES is presented. Some chaotic complex systems were also used for the construction of the S-Box in [7] by H. Lui, A. Kadir, and P. Gong. Ali et al. [8] introduced an effective method that makes use of the Möbius transformation and the combination of Frobenius automorphism. This gave us two very nonlinear permutations with a very high cryptographic strength that can generate millions of S-boxes. By elucidating the conditions for producing unique S-boxes and guaranteeing that the generated S-boxes possess a consistent probability distribution, the dynamic behavior of the suggested generator is examined. The design methodology used in study [9] is robust and satisfies S-box security and performance criteria. The work presents a novel 1D hybrid chaotic map, which is subsequently utilized to construct an S-box design with finite fields of degrees 4 and 8. A straightforward technique is developed to get rid of any possible problems with the suggested approach. The proposed method produces powerful S-boxes with an average nonlinearity of over 111.5. The authors in [10] provided a novel S-box generation approach based on the reinforcement of randomness generated from the metastable states of the R-S latch. The suggested technique employs an FPGA chip to acquire design inputs based on physical reality at the hardware level. Blake2b, Blake2s, SHA3, and Shake are the four hash algorithms that are used to convert design inputs with low statistical adequacy into S-boxes. To address various S-Box limitations, such as low nonlinearity, fixed point, reverse fixed point, and short iteration period rings, a non degenerate 2D-Hyper chaotic Map (2D-HCM) is initially developed, and its dynamical behavior is analyzed [11]. According to the initial trials of the randomness test, the two pairs of sequences produced by the 2D-HCM algorithm, when merged, show decent levels of incomprehensibility. Thereafter, a simple S-box was formed using the generalized multiplicative inverse of each of the coordinates of a point on an elliptic curve defined over a finite field. The initial S-Box values are permuted according to the index sequence generated by the 2D-HCM, thus a more robust S-Box is obtained, which supplants the shortcomings of the initial S-Box. The authors of [12] presented an elucidative procedure of forming dynamic S-boxes, which is centered on a certain type of hyper elliptic curves defined on prime finite fields. The suggested algorithm that will recover the valid points of an elliptic-curve cryptosystem is one that works by initializing a large prime number n, as well as a random number r. It proceeds to fix a known filtering condition on each coin-toss-point on the curve. The modular reduction mechanism is used along with the consideration of the two-dimensional one, so that each point could be surveyed, and the list of different values could be compiled. Farooq et al. [13] presented a non-degenerate 2D enhanced quadratic map (2DEQM) with a very high unpredictability and ergodicity.To obtain a collection of extremely non-linear S-boxes, the affine transformation matrices and affine transformation constants were designed, and those elements of the transformations were then implemented on the original S-boxes. The properties of the S-boxes thus obtained were validated by intensive statistical analysis tests. This paper [14] introduces a new design methodology of S-box where DNA-based biological elements are combined with a large parameter space covered by a 2D hyper-chaotic Schaffer map (SM). In order to authenticate the intended method, copious simulation tests were conducted to check the nonlinearity and the resistance to the attack by differential power analysis (DPA) of the resulting S-box. As shown in the experimental results, the proposed S-box has high nonlinearity and is quite resistant to DPA as compared to several of its counterparts that have their technological state in the art.
Cryptographers and researchers desire S-Boxes that balance between security, non-linearity, and both computability by human beings and software efficiency. An in-depth analysis, simulation-based, and cryptographic analysis are the usual criteria used to analyze and validate S-Boxes used in a cryptographic algorithm. Cryptographers perform in-depth examinations, implementations, and contrast with voltage S-boxes, to obtain the most suitable S-box selection of a particular cryptography algorithm. Cryptanalysis is the process of searching for flaws and vulnerabilities in the S-Box of the known attacks. Differential cryptanalysis, linear cryptanalysis, algebraic attacks, and other methods of cryptographic analysis have been widely used to check how vulnerable the S-Box becomes to these attacks. Non-linearity and Confusion, Bit Independence criteria, Avalanche Criteria, differential approximation, and linear approximation probability are some of the tests to check the strength and invulnerability of an S-box.
Although numerous methods have been proposed for the construction of substitution boxes (S-boxes) in block ciphers—such as those based on algebraic structures, chaos theory, finite field inversion (e.g., AES), and combinatorial optimization—there remains a gap in the exploration of S-boxes derived from fractional linear transformations over Galois fields with customized parameters. Most existing works either rely on fixed inversion functions (as in AES) or chaotic maps that lack rigorous algebraic structure and predictability. Additionally, the interplay between algebraic transformations and their impact on cryptographic criteria (such as nonlinearity, bijectively, and resistance to linear and differential attacks) has not been extensively studied in the context of parametric transformations like \(\dfrac{1}{ax+b}\) over \(GF(2^{8})\). The proposed method enables tunability through parameters \(a \& b\) and provides a mathematically grounded alternative to heuristic or empirically derived designs.
Consider the irreducible polynomial \(p(x)=x^8+x^7+x^6+x^5+x^2+x+1\) over \(\mathbb{Z}_2\) and the maximal ideal \((p(x))\) in \(\mathbb{Z}_2[x]\), we have Galois Field \(GF(2^8)\) given by \[\begin{aligned} GF(2^8)=\frac{\mathbb{Z}_2[x]}{(p(x))}&=& \left\{a_0+a_1t+a_2t^2+…+a_7t^7 | a_0+,a_1,…,a_7 \in \mathbb{Z}_2\right\}\\ &=&<s | s^{255}=1> \cup \{0\}, \end{aligned}\] where \(t\) is the particular root of \(p(x)\) and \(s\) is the generator of the cyclic group \((GF(2^8))^*=GF(2^8)-\{0\}\) under multiplication.
Define a function \(f:GF(2^8) \to GF(2^8)\) by \[\zeta(x)= \begin{cases} \dfrac{1}{ax+b} & x\ne \frac{b}{a},\\ 0 & x=\frac{b}{a}, \end{cases}\] where \(a, b \in GF(2^8)\) and \(a\neq 0\). It can easily be seen that \(f\) is bijective. The elements of \(GF(2^8)\) in decimal, powers of \(s\) and polynomial forms are given in Table 1, and the images of \(GF(2^8)\) under \(f\) in the form of proposed S-box are given in Table 2 by selecting \(a=8\) and \(b=9\).
| Power | Decimal | Polynomial | Power | Decimal | Polynomial | Power | Decimal | Polynomial |
|---|---|---|---|---|---|---|---|---|
| 0 | 1 | 0 | 1 | 2 | 1 | 2 | 4 | 2 |
| 3 | 8 | 3 | 4 | 16 | 4 | 5 | 32 | 5 |
| 6 | 64 | 6 | 7 | 128 | 7 | 8 | 231 | 765210 |
| 9 | 41 | 530 | 10 | 82 | 641 | 11 | 164 | 752 |
| 12 | 175 | 753210 | 13 | 185 | 75430 | 14 | 149 | 7420 |
| 15 | 205 | 76320 | 16 | 125 | 654320 | 17 | 250 | 765431 |
| 18 | 19 | 410 | 19 | 38 | 521 | 20 | 76 | 632 |
| 21 | 152 | 743 | 22 | 215 | 764210 | 23 | 73 | 630 |
| 24 | 146 | 741 | 25 | 195 | 7610 | 26 | 97 | 650 |
| 27 | 194 | 761 | 28 | 99 | 6510 | 29 | 198 | 7621 |
| 30 | 107 | 65310 | 31 | 214 | 76421 | 32 | 75 | 6310 |
| 33 | 150 | 7421 | 34 | 203 | 76310 | 35 | 113 | 6540 |
| 36 | 226 | 7651 | 37 | 35 | 510 | 38 | 70 | 621 |
| 39 | 140 | 732 | 40 | 255 | 76543210 | 41 | 25 | 430 |
| 42 | 50 | 541 | 43 | 100 | 652 | 44 | 200 | 763 |
| 45 | 119 | 654210 | 46 | 238 | 765321 | 47 | 59 | 54310 |
| 48 | 118 | 65421 | 49 | 236 | 76532 | 50 | 63 | 543210 |
| 51 | 126 | 654321 | 52 | 252 | 765432 | 53 | 31 | 43210 |
| 54 | 62 | 54321 | 55 | 124 | 65432 | 56 | 248 | 76543 |
| 57 | 23 | 4210 | 58 | 46 | 5321 | 59 | 92 | 6432 |
| 60 | 184 | 7543 | 61 | 151 | 74210 | 62 | 201 | 7630 |
| 63 | 117 | 65420 | 64 | 234 | 76531 | 65 | 51 | 5410 |
| 66 | 102 | 6521 | 67 | 204 | 7632 | 68 | 127 | 6543210 |
| 69 | 254 | 7654321 | 70 | 27 | 4310 | 71 | 54 | 5421 |
| 72 | 108 | 6532 | 73 | 216 | 7643 | 74 | 87 | 64210 |
| 75 | 174 | 75321 | 76 | 187 | 754310 | 77 | 145 | 740 |
| 78 | 197 | 7620 | 79 | 109 | 65320 | 80 | 218 | 76431 |
| 81 | 83 | 6410 | 82 | 166 | 7521 | 83 | 171 | 75310 |
| 84 | 177 | 7540 | 85 | 133 | 720 | 86 | 237 | 765320 |
| 87 | 61 | 54320 | 88 | 122 | 65431 | 89 | 244 | 76542 |
| 90 | 15 | 3210 | 91 | 30 | 4321 | 92 | 60 | 5432 |
| 93 | 120 | 6543 | 94 | 240 | 7654 | 95 | 7 | 210 |
| 96 | 14 | 321 | 97 | 28 | 432 | 98 | 56 | 543 |
| 99 | 112 | 654 | 100 | 224 | 765 | 101 | 39 | 5210 |
| 102 | 78 | 6321 | 103 | 156 | 7432 | 104 | 223 | 7643210 |
| 105 | 89 | 6430 | 106 | 178 | 7541 | 107 | 131 | 710 |
| 108 | 225 | 7650 | 109 | 37 | 520 | 110 | 74 | 631 |
| 111 | 148 | 742 | 112 | 207 | 763210 | 113 | 121 | 65430 |
| 114 | 242 | 76541 | 115 | 3 | 10 | 116 | 6 | 21 |
| 117 | 12 | 32 | 118 | 24 | 43 | 119 | 48 | 54 |
| 120 | 96 | 65 | 121 | 192 | 76 | 122 | 103 | 65210 |
| 123 | 206 | 76321 | 124 | 123 | 654310 | 125 | 246 | 765421 |
| 126 | 11 | 310 | 127 | 22 | 421 | 128 | 44 | 532 |
| 129 | 88 | 643 | 130 | 176 | 754 | 131 | 135 | 7210 |
| 132 | 233 | 76530 | 133 | 53 | 5420 | 134 | 106 | 6531 |
| 135 | 212 | 7642 | 136 | 79 | 63210 | 137 | 158 | 74321 |
| 138 | 219 | 764310 | 139 | 81 | 640 | 140 | 162 | 755 |
| 141 | 163 | 7510 | 142 | 161 | 750 | 143 | 165 | 7520 |
| 144 | 173 | 75320 | 145 | 189 | 754320 | 146 | 157 | 74320 |
| 147 | 221 | 764320 | 148 | 93 | 64320 | 149 | 186 | 75431 |
| 150 | 147 | 7410 | 151 | 193 | 760 | 152 | 101 | 6520 |
| 153 | 202 | 7631 | 154 | 115 | 65410 | 155 | 230 | 76521 |
| 156 | 43 | 5310 | 157 | 86 | 6421 | 158 | 172 | 7532 |
| 159 | 191 | 7543210 | 160 | 153 | 7430 | 161 | 213 | 76420 |
| 162 | 77 | 6320 | 163 | 154 | 7431 | 164 | 211 | 76410 |
| 165 | 65 | 60 | 166 | 130 | 71 | 167 | 227 | 76510 |
| 168 | 33 | 50 | 169 | 66 | 61 | 170 | 132 | 72 |
| 171 | 239 | 7653210 | 172 | 57 | 5430 | 173 | 114 | 6541 |
| 174 | 228 | 7652 | 175 | 47 | 53210 | 176 | 94 | 64321 |
| 177 | 188 | 75432 | 178 | 159 | 743210 | 179 | 217 | 76430 |
| 180 | 85 | 6420 | 181 | 170 | 7531 | 182 | 179 | 75410 |
| 183 | 129 | 70 | 184 | 229 | 76520 | 185 | 45 | 5320 |
| 186 | 90 | 6431 | 187 | 180 | 7542 | 188 | 143 | 753210 |
| 189 | 249 | 765430 | 190 | 21 | 420 | 191 | 42 | 531 |
| 192 | 84 | 642 | 193 | 168 | 753 | 194 | 183 | 754210 |
| 195 | 137 | 730 | 196 | 245 | 765420 | 197 | 13 | 320 |
| 198 | 26 | 431 | 199 | 52 | 542 | 200 | 104 | 653 |
| 201 | 208 | 764 | 202 | 71 | 6210 | 203 | 142 | 7321 |
| 204 | 251 | 7654310 | 205 | 17 | 40 | 206 | 34 | 51 |
| 207 | 68 | 62 | 208 | 136 | 73 | 209 | 247 | 7654210 |
| 210 | 9 | 30 | 211 | 18 | 41 | 212 | 36 | 52 |
| 213 | 72 | 63 | 214 | 144 | 74 | 215 | 199 | 76210 |
| 216 | 105 | 6530 | 217 | 210 | 7641 | 218 | 67 | 610 |
| 219 | 134 | 721 | 220 | 235 | 765310 | 221 | 49 | 540 |
| 222 | 98 | 651 | 223 | 196 | 762 | 224 | 111 | 653210 |
| 225 | 222 | 764321 | 226 | 91 | 64310 | 227 | 182 | 75421 |
| 228 | 139 | 7310 | 229 | 241 | 76540 | 230 | 5 | 20 |
| 231 | 10 | 31 | 232 | 20 | 42 | 233 | 40 | 53 |
| 234 | 80 | 64 | 235 | 160 | 75 | 236 | 167 | 75210 |
| 237 | 169 | 7530 | 238 | 181 | 75420 | 239 | 141 | 7320 |
| 240 | 253 | 7654320 | 241 | 29 | 4320 | 242 | 58 | 5431 |
| 243 | 116 | 6542 | 244 | 232 | 7653 | 245 | 55 | 54210 |
| 246 | 110 | 65321 | 247 | 220 | 76432 | 248 | 95 | 643210 |
| 249 | 190 | 754321 | 250 | 155 | 74310 | 251 | 209 | 7640 |
| 252 | 69 | 620 | 253 | 138 | 731 | 254 | 243 | 765410 |
| – | 0 | zero polynomial |
| 119 | 1 | 144 | 63 | 110 | 61 | 171 | 203 | 20 | 15 | 147 | 6 | 140 | 241 | 161 | 235 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | 108 | 7 | 159 | 19 | 121 | 58 | 239 | 168 | 223 | 187 | 16 | 206 | 221 | 102 | 97 |
| 247 | 224 | 90 | 176 | 233 | 91 | 107 | 111 | 85 | 114 | 64 | 99 | 252 | 226 | 24 | 98 |
| 41 | 249 | 251 | 68 | 202 | 210 | 109 | 56 | 13 | 167 | 208 | 229 | 191 | 81 | 211 | 44 |
| 155 | 215 | 79 | 86 | 0 | 69 | 209 | 158 | 212 | 124 | 43 | 77 | 190 | 50 | 152 | 11 |
| 76 | 201 | 246 | 137 | 95 | 59 | 25 | 80 | 230 | 164 | 213 | 52 | 106 | 18 | 62 | 179 |
| 255 | 165 | 40 | 193 | 220 | 177 | 238 | 199 | 123 | 204 | 183 | 145 | 38 | 116 | 151 | 14 |
| 31 | 48 | 170 | 128 | 53 | 214 | 9 | 180 | 153 | 65 | 26 | 71 | 115 | 218 | 82 | 17 |
| 198 | 228 | 196 | 35 | 135 | 39 | 222 | 182 | 45 | 169 | 88 | 162 | 136 | 21 | 112 | 67 |
| 12 | 30 | 49 | 5 | 126 | 2 | 113 | 122 | 32 | 89 | 194 | 93 | 217 | 216 | 57 | 242 |
| 197 | 127 | 28 | 232 | 101 | 173 | 105 | 133 | 142 | 130 | 34 | 83 | 231 | 96 | 143 | 75 |
| 154 | 248 | 22 | 100 | 172 | 73 | 219 | 138 | 104 | 175 | 129 | 36 | 245 | 117 | 160 | 118 |
| 166 | 227 | 150 | 192 | 55 | 254 | 237 | 189 | 72 | 185 | 236 | 234 | 200 | 23 | 243 | 146 |
| 163 | 181 | 134 | 42 | 70 | 47 | 139 | 78 | 186 | 178 | 3 | 87 | 10 | 60 | 244 | 4 |
| 29 | 37 | 132 | 125 | 250 | 74 | 207 | 148 | 240 | 225 | 188 | 253 | 92 | 205 | 54 | 66 |
| 51 | 149 | 195 | 46 | 103 | 33 | 157 | 27 | 174 | 131 | 8 | 120 | 84 | 141 | 156 | 94 |
In this section of the article, we present an assessment of the defensive capabilities of our proposed S-box to address potential cryptographic vulnerabilities. The S-box, referred to as Table 2, underwent rigorous testing, the details of which are provided towards the end of the introduction. The obtained results were subsequently compared against those of established S-boxes. The forthcoming section outlines the methodology employed for conducting these tests.
The term “nonlinearity” was coined by Pieprzyk and Finkelstein in 1988, [15], to capture the disparity between the \(n^{th}\) variable Boolean function, say \(g\), and the set of all affine functions involving \(n\) variables. It serves as a measure of dissimilarity. The maximum attainable nonlinearity for S-boxes constructed using \(GF(2^8)\) is 120. While the literature thus far has achieved a nonlinearity pinnacle of 112, our S-box exhibits an identical nonlinearity value.
This test measures the extent of variation to which an output changes by a tiny alteration in the input value. The SAC was developed by Tavares and Webster [16]. As per the SAC’s findings, if a single input bit of the S-box is flipped, precisely \(50\%\) of the output bits should flip, on average. The formula for the dependence matrix \(M\) that is needed for the SAC is as follows: \[M(x)=\frac{\sum\limits_{k=1}^{8}h(x)\oplus h(x \oplus y_{j})}{256} \quad \,\, HWT(y_j)=1 \hspace{0.5cm} \forall \hspace{0.2cm} j=1, 2, … ,8.\]
The BIC of an S-box measures the cryptographic strength of an S-box. It evaluates the extent to which the output bits of an S-box are independent of the input bits. A higher degree of independence between input and output bits is desirable as it makes it harder for attackers to analyze and break the Encryption system.
LAP test is a form of cryptanalysis that is deployed to assess the robustness of an S-box within a block cipher [17]. The LAP test estimates the likelihood that there is a linear relationship between the input and output bits of an S-box. The LAP test measures the S-box through its relation between its input and output bits. It uses a statistical formula to quantify this relationship. Pearson correlation coefficient gives a numerical measure of how linear the input and output bits of an S-box are. \[LAP = \max_{x,y \neq 0} \left| \frac{\left| \left\{ \alpha \in GF(2^8) | x.\alpha=y.S(\alpha) \right\} \right|-128}{256} \right|.\]
The DAP test measures the difference in the probability using a random sample in the context of statistical inquiry. Instead of measuring all possible combinations of inputs, the procedure identifies a subset of pairs to be measured and summarizes the proportion of pairs that exhibit the designated differential association. More precisely, when it comes to estimating the differential probabilities, it is noticed that the smaller the subset is, the less accurate the estimate can be obtained. The DAP test is commonly used along with the LAP test as a method of security analysis of an S-box.
\[DP(\Delta t,\Delta u)=\frac{|\{t \in GF(2^8)~|~S(t)\oplus S(t\oplus \Delta t)=\Delta u\}|}{256},\] where \(\Delta t\) and \(\Delta u\) represents the input and output differential respectively.
| S-box | NL | SAC | BIC-NL | BIC-SAC | LAP | DAP |
|---|---|---|---|---|---|---|
| Proposed S-box | 112 | 0.4995 | 112 | 0.5039 | 0.0625 | 0.0156 |
| APA | 112 | 0.5 | 112 | 0.499 | 0.062 | 0.0156 |
| Gray | 112 | 0.499 | 112 | 0.502 | 0.062 | 0.0156 |
| \(S_{8}\) AES | 112 | 0.504 | 112 | 0.502 | 0.062 | 0.0156 |
| Skipjack | 105.75 | 0.503 | 104.14 | 0.499 | 0.109 | 0.0468 |
| Residue prime | 99.5 | 0.515 | 101.71 | 0.502 | 0.132 | 0.281 |
| [18] | 106.75 | 0.5032 | 103.6429 | 0.5074 | 0.1484 | 0.0469 |
| [1] | 112 | 0.5049 | 112 | 0.5046 | 0.062 | 0.0156 |
| [19] | 105.5 | 0.507 | 106 | 0.462 | 0.140 | 0.0242 |
| [20] | 104.87 | 0.493 | 99 | 0.504 | 0.105 | 0.0390 |
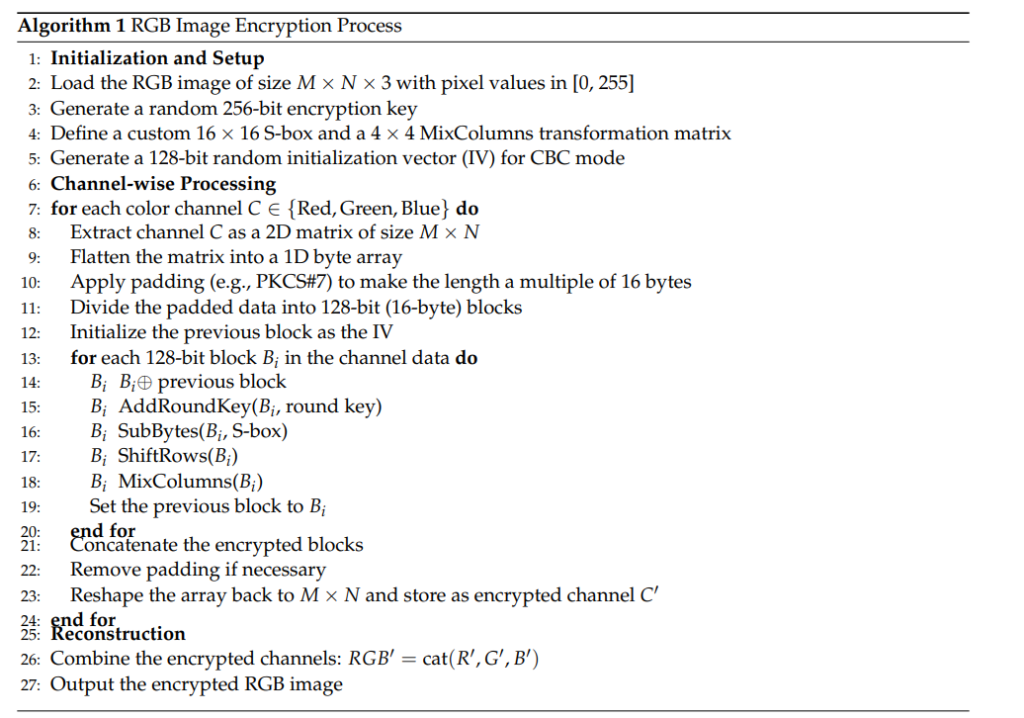
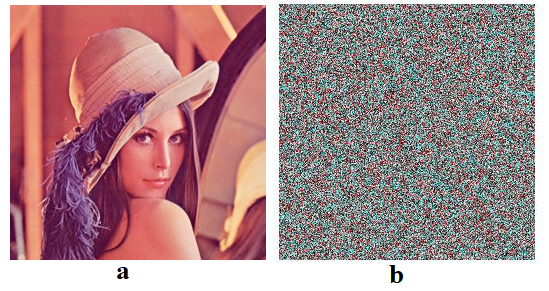
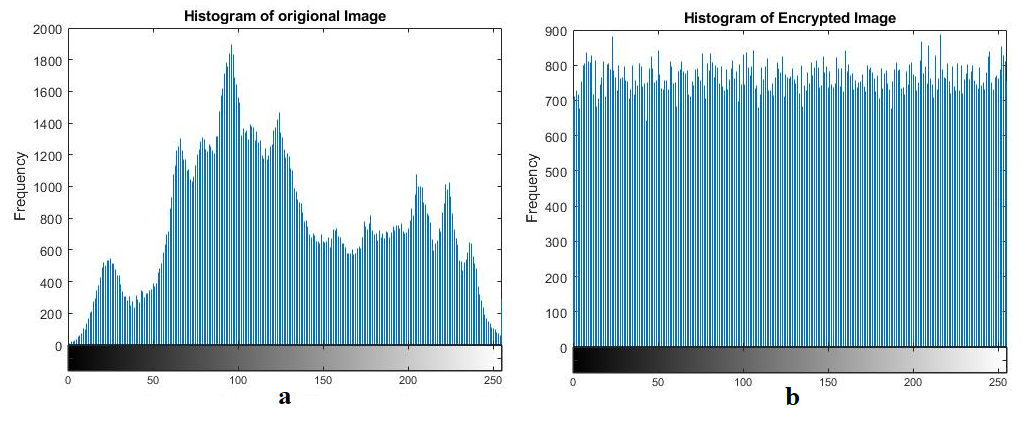
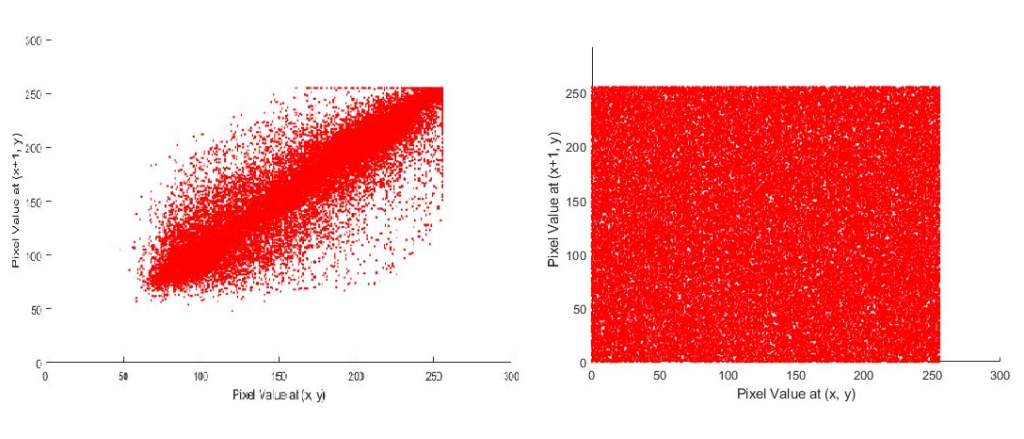
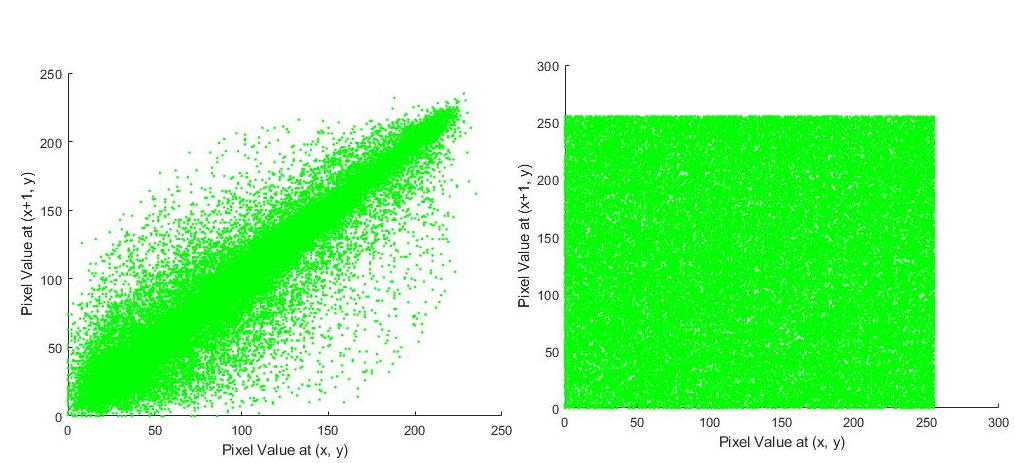
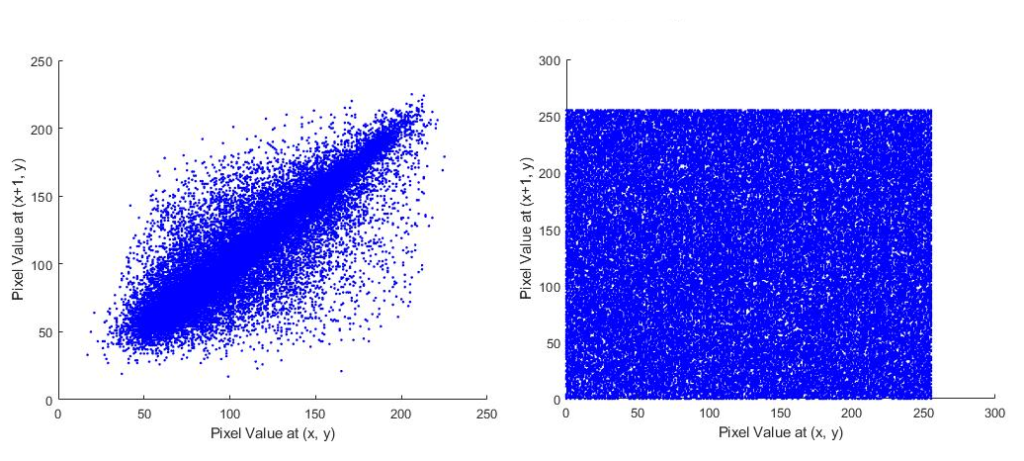
We have employed our S-box to encrypt various images in this segment. To evaluate the efficacy of the algorithm used for the encryption of an image, we utilized the majority logic criterion which comprises Contrast, Entropy, Correlation, Energy, Homogeneity, Mean Square Error, Peak Signal to Noise Ratio, Normalized Cross-Correlation, Average Difference, Structural Content, Maximum Difference, Normalized Absolute Error, Root Mean Square Error, Universal Quality Index, Mutual Information, Structural Similarity, Number of Pixel Change Rate, and Unified Average Changing Intensity. The figures are displayed in Figure 1, 2, 3, 4, 5 and Table 4.
| Entropy | Correlation | NPCR | UACI | PSNR | MSE | |
|---|---|---|---|---|---|---|
| Proposed Scheme | 7.9978 | -0.00033187 | 99.60 | 33.46 | 28.0112 | 10566.1790 |
| [21] | 7.9994 | -0.0031 | – | – | – | – |
| AES | 7.7302 | 0.0879 | – | – | – | – |
| \(S_{8}\) AES | 7.7095 | 0.2310 | – | – | – | – |
| [22] | 7.9970 | 0.00073 | – | – | 8.6554 | 8972.7887 |
Entropy is a fundamental notion frequently employed within the realm of cryptographic image encryption. Randomness is defined as the extent of non-homogeneity, or lack of pattern, displayed by the pixels of an image. To be more exact, it refers to the quantity of random noise (uncontrollable alterations in the pixel values) present in the particular image. In the process of encrypting an image, a high level of entropy in the ciphertext is a critical aspect. The entropy value of an image can be derived by employing the following formula. \[H = -\sum\limits_{i=1}^n(p_i\log_2(p_i)).\]
In the given context, \(H\) represents the entropy measure, while \(p\) indicates the probability associated with the occurrence of individual pixel values within the image.
Correlation allows us to talk about the degree of association between any two variables. In image encryption, correlation is used as a unit of measuring the level of dependency between neighboring pixels of an image. By empirical research, it was determined that the higher the correlation value of the pixels that are near each other, the stronger the spatial interdependence is, which is the property capable of threatening the security of an encrypted picture and increasing its attackability. \[r_{ab} = \frac{\sum\limits_{i=1}^n(a_i – \bar{a})(b_i – \bar{b})}{\sqrt{\sum\limits_{i=1}^n(a_i – \bar{a})^2} \sqrt{\sum\limits_{i=1}^n(b_i – \bar{b})^2}}.\]
Within this context, the correlation coefficient \(r_{ab}\) signifies the measure of correlation between the variables \(a\) and \(b\). This measure provides quantitative ideas of how strong the association between the two variables is and in what direction it is headed.
Homogeneity by its name refers to similarities between pixels on a local scale. Consequently large value determines strong relationship in neighboring pixels while low implies more dissimilarity. Homogeneity can be calculated by the following formula \[H = \frac{1}{1 +\sum\limits_{x=1}^{m} \sum \limits_{y=1}^{m}\frac{(x-y)^{2}}{m^{2}}}.\]
Energy is the sum of the data or signal strength detected in an image. There will be a substantial amount of information or detail in an image that is highly energetic, and this will generate a large amount of squares. Conversely, a low-energy image will present a modest sum of squares, indicating a scarcity of information or minimal detail. The following formula calculate the energy \[E = \sum\limits_{x=1}^{m} \sum\limits_{y=1}^{n} GLCM(x,y)^{2}.\]
The contrast of an image relates to the identifiable difference in the brightness or intensity of the darkest and lightest parts. A high contrast image will also have a large difference in intensity whereas a low contrast image will have a relatively smaller difference. Contrast determine the capacity of estimating the strength of an image to withstand many attacks. When an encrypted image has high contrast, then it is painful to an attacker to identify certain parts of the image or insert hidden information inside the image. \[Cont.=\sum\limits_{x}\sum\limits_{y} (x-y)^2 f(x,y).\]
Within the specified context, the variables \(x\) and \(y\) correspond to the pixels present in the image. The function \(f(x,y)\) represents the probability that two neighboring pixels in the image possess identical gray levels.
MSE is a metric commonly used in image processing and computer vision tasks to assess the quality of image encryption protocols. MSE quantifies the mean square deviation among the pixel values of the original image and the encrypted image. Here’s how TO calculate the MSE for image encryption. \[MSE=\frac{1}{m\times n}\sum\limits_{x=1}^{m} \sum\limits_{y=1}^{n} [O(x,y)-E(x,y)]^{2},\] whereas \(O(x, y)\) is the plain image, \(E(x, y)\) is the ciphered version, and m, n are respectively the dimensions of these images. The Mean-squared error (MSE) measure provides a numeric measure of the distortion that the encryption scheme adds to a message. The lower the mean-square-error (MSE), the less the distortion and hence the better the encryption.
The other metric that is usually used to determine the effectiveness of image encryption algorithms is PSNR. It quantifies the proportionality between the signal’s maximum potential power (in this case, the original image) and the power of the distortion introduced by the encryption process (in this case, the encrypted image). Compute the PSNR using the formula: \[\text{PSNR} = 10\cdot \log_{10}\left(\frac{{\text{{max\_pixel\_value}}^2}}{{\sqrt{{MSE}}}}\right),\] where MSE is the Mean Squared Error calculated as described in the previous answer. The PSNR value represents the quality of the encrypted image. Higher PSNR values indicate lower distortion and hence better encryption quality.
It is a measure used in image processing and computer vision tasks, including image encryption. It quantifies the resemblance between two images by calculating the correlation coefficient between their pixel intensities. Here’s the formula to calculate the NCC for image encryption \[NCC = \sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n}\frac{{ O(x, y) \times E(x, y)}}{{\sqrt{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} I(x, y)^2}}},\] whereas \(O(x, y)\) is for plain image, \(E(x, y)\) is for ciphered version and \(m, n\) are respectively the dimensions of these images.The resulting value represents the NCC between the original and encrypted images. NCC can be used as a metric to assess the quality of image encryption algorithms. Higher NCC values indicate a higher degree of similarity between the original and encrypted images, suggesting better encryption quality.
To calculate the average difference in image encryption, you need to compare the pixel values between the original image and the encrypted image. It provides a measure of the overall dissimilarity or change between the original and encrypted images. Here’s the formula \[\text{AD} = \frac{{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} (O(x, y) – E(x, y))}}{{M \times N}},\] whereas \(O(x, y)\) is the plain image, \(E(x, y)\) is the ciphered version and \(m, n\) are respectively the dimensions of these images.
In the context of image encryption, the term “structural content” refers to the preservation of the essential visual features, patterns, and structures in an encrypted image. It is desired that the encrypted image retains the key visual information or structural content of the original image while making it difficult for unauthorized individuals to interpret or extract meaningful information. Preserving structural content in image encryption is important because it allows the encrypted image to maintain its visual integrity and facilitates tasks such as image recognition, object detection, or visual analysis even in the encrypted domain. \[\text{SC} = \frac{{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} O(x, y)^2}}{{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} E(x, y)^2}}.\]
It provides a measure of the largest discrepancy or change between the original and encrypted images. The encrypted difference of images can be defined as the greatest absolute difference between matching pixel values between the original and the encrypted image. The formula to compute the maximum difference is \[MD=max|O(x,y)-E(x,y)|.\]
NAE is used as a measure to evaluate the difference between the intensity of the pixel in the source images and that in the encrypted images. It gives a normalized value of the mean difference between the values of the corresponding pixels. The formula for Normalized Absolute Error in image encryption is as follows \[\text{NAE} = \frac{{\sum\limits_{x=1}^{n} \sum\limits_{y=1}^{m} |O(x, y) – E(x, y)|}}{{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} |O(x, y)|}}.\]
It offers an estimation of the mean of the differences between the related pixel values, considering both the magnitude of what is in error and the distribution of the error. RMSE gives an indication of the average difference between the original and encrypted image pixel by pixel. The formula for RMSE in image encryption is as follows \[\text{RMSE} = \sqrt{\frac{\sum\limits_{y=1}^{m} \sum\limits_{x=1}^{n} [O(x, y) – E(x, y)]^2}{m \times n} }.\]
Many aspects are put into consideration by UQI including luminance, contrast, and structure similarity. UQI gives an indicator of how similar or good a pair of original and the encrypted images are. The following expression represents the formula used to calculate the Universal Quality Index in the context of image encryption \[\text{UQI}(O, E) = \frac{{4 \mu_{O} \mu_{E} \mu_{OE}}}{{({\mu_o}^2-{\mu_E}^2) ({\sigma_o}^2-{\sigma_E}^2)}},\] where \(\mu_{O}, \mu_{E}\) indicates the mean values of plain and distorted images and \(\sigma_{O}, \sigma_{E}\) denote the standard deviation of plain and scrambled images.
Mutual Information gives a quantitative expression of the statistical correlation or carried information between the original and encrypted image. It may provide an evaluation of the quality or quality of image encryption algorithms by providing an evaluation of the integrity of significant information. The formula for Mutual Information in image encryption is \[\text{MI}(I, C) = \sum\limits_{y \in C} \sum\limits_{x \in I} p(x, y) \log_2 \left( \frac{p(x, y)}{p(x) \cdot p(y)}\right),\] whereas \(p(x, y)\) is the joint probability function of \(O\) and \(E\), further \(p(x)\) and \(p(y)\) are respectively the marginal probability distribution functions of \(O\) and \(E\).
It is the commonly used indicator to evaluate the perception quality and visual similarity between two images. It quantifies the structural similarity between original and ciphered images by taking into consideration the luminance, contrast and structural information. The greater the value of SSIM, the more they are similar, and the higher is the estimated image quality difference. The measure amidst two windows \(x\) and \(y\) of common size \(n \times n\) is \[\text{SSIM}(x, y) = \frac{{(2 \mu_{y} \mu_{y} + c_{1}) (2 \sigma_{xy} + c_{2})}}{{(\mu^{2}_{x} + \mu^{2}_{y} + c_{1}) \cdot (\sigma^{2}_{x} + \sigma^{2}_{y} + c_{2})}},\] where \(\mu_{x}\) is the average of \(x\), \(\mu_{2}\) is the average of \(y\), \(\sigma^{2}_{x}\) is the variance of \(x\), \(\sigma^{2}_{y}\) is the variance of \(y\), \(\sigma_{xy}\) is the covariance of \(x\) and \(y\), \(c_{1} = (k_{1} l)^2\) and \(c_{2} = (k_{2} l)^2\) are the variables to stabilize the division with weak denominator, \(l\) is the dynamic range of the pixel values, \(k_{1} = 0.01\) and \(k_{2} = 0.03\) by default.
It determine how encrypting an entire image can be different by the process of changing a single pixel within an input image by counting the number of pixels that varied in the resultant ciphertext after a perturbation to a single pixel in input image. NPCR is particularly useful when comparing two encrypted images, denoted as \(I_1\) and \(I_2\) having dimensions \(m\times n\), respectively, wherein both images differ by only one pixel. NPCR can be calculated by performing the following measurement \[NPCR = \frac{{\sum\limits_{i,j} M(i,j)}}{{m \times n}},\] where \(M(i,j) = \begin{cases} 0, & \text{if } I_1(i,j) = I_2(i,j), \\ 1, & \text{if } I_1(i,j) \neq I_2(i,j). \end{cases}\)
The UACI (universal average crossing intensity) is a measurement of the average difference in the intensity of the pixels in a source image and their respective pixel in the encrypted image [12]. The UACI parameter measures the average extent of changing pixel-intensity values in the course of encryption process. A small UACI value will mean that the image has very little average change to its value and therefore close to tonal consistency; a higher UACI value will mean that the image has greater difference to its value and will be representing a greater change in luminance. \[UACI = \frac{1}{{m \times n}} \sum\limits_{i,j} \frac{{|I_1(i, j) – I_2(i, j)|}}{{255}},\] whereas \(I_1, I_2,m,n\) are defined in NPCR.
Key sensitivity analysis is one of the most essential factors of encrypting an image, because it determines how small alterations in the encryption key are going to affect the encrypted image. A strong test of resilience and security attributes of an encryption algorithm in the face of the changes in the key is necessary. In key-sensitive image analysis, a given plaintext image is encrypted multiple times with a different key each time a different ciphertext image is output. These individual ciphertext images are then compared in a systematic manner in order to find salient features, which are consistent across the images.It is also a desirable cryptographic characteristic that an algorithm has a strong response to minor changes in key parameter. Therefore, determining relative key sensitivity, is a compelling conventional requirement in diagnosing the strength of a specific encryption scheme. See Table 5 for texture analysis for original and encrypted lena image and see Table 6 for image quality measures for lena image.
| Orignal Image | Cipher Image | |||||
|---|---|---|---|---|---|---|
| Red | Green | Blue | Red | Green | Blue | |
| Contrast | 0.5228 | 0.5650 | 0.5011 | 10.5348 | 10.5589 | 10.5754 |
| Homogenity | 0.8460 | 0.8449 | 0.8490 | 0.3876 | 0.38865 | 0.38744 |
| Entropy | 7.3039 | 7.6153 | 7.0690 | 7.9979 | 7.9978 | 7.9979 |
| Correlation | 0.896406 | 0.902091 | 0.805095 | -0.00033187 | -0.002805 | -0.0021585 |
| Energy | 0.1266 | 0.0893 | 0.1531 | 0.0156 | 0.0156 | 0.0156 |
| Chi-Square | – | – | – | 269.1094 | 273.4219 | 273.4219 |
| Encrypted Image | Optimal Values | |||||
|---|---|---|---|---|---|---|
| Quality Name | Red | Green | Blue | |||
| MSE | 10566.1790 | 9043.6368 | 7143.4926 | 10057.2 | 9898.89 | 6948.19 |
| PSNR | 28.0112 | 28.3491 | 28.8613 | 8.1060 | 8.1749 | 9.7120 |
| NK | 0.6618 | 1.0087 | 1.1044 | 0.6725 | 1.0031 | 1.0923 |
| AD | 84 | 78 | 70 | 50.0448 | 31.4276 | 19.7989 |
| SC | 1.6290 | 0.5805 | 0.5745 | 1.5787 | 0.5582 | 0.5711 |
| MD | 249 | 227 | 204 | 236 | 210 | 210 |
| NAE | 0.3295 | 0.3061 | 0.2775 | 0.4537 | 0.8310 | 0.6628 |
| RMSE | 102.7919 | 95.0980 | 84.5192 | 100.286 | 99.4932 | 83.3558 |
| UQI | -0.0002 | -0.0009 | -0.0038 | -0.0050 | -0.0077 | 0.0107 |
| MI | 0.56425 | 0.65967 | 0.46235 | 5.6534 | 7.2283 | 6.0723 |
| SSIM | 0.0067238 | 0.0059492 | 0.0048311 | 0.0078 | 0.0053 | 0.0187 |
Since S-box structures are frequently the fundamental building blocks of cryptographic algorithms, research has been done to investigate how modifications to their architecture affect their robustness. S-box structures strive to raise the bar for cryptographic security and offer robust protection against emerging threats. The application of the devised bijective mapping on the elements of the Galois Field \(GF(2^8)\) facilitated the development of an S-box as discerned from the discourse above. These results demonstrate that the use of S-boxes in block cipher systems can enhance security against sophisticated attacks, such as linear and differential cryptanalysis. The resulting S-boxes outperformed key cryptographic parameters, such as low differential probability and high nonlinearity values. Comparisons to related studies demonstrate that our proposed method performs better than existing approaches in basic security criteria such as SAC, BIC, and NL. With our carefully devised substitution box, we encrypted Lena’s image. Subsequently, we presented the encrypted images alongside their respective histograms and showed the texture analysis of both the original and ciphered images. Also, the results for the image quality measure were given, which collectively serve as tangible proof illustrating the outstanding capabilities of our S-box. These visual demonstrations effectively reinforce the conviction that our S-box is an exemplary choice for cryptographic operations. We would like to investigate the design of S-boxes in the future, utilizing optimization models, algebraic transformations, and chaos theory.
Daemen, J., & Rijmen, V. (2002). The Design of Rijndael (Vol. 2). New York: Springer-verlag.
Tran, M. T., Bui, D. K., & Duong, A. D. (2008, December). Gray S-box for advanced encryption standard. In 2008 International Conference on Computational Intelligence and Security (Vol. 1, pp. 253-258). IEEE.
Cui, L., & Cao, Y. (2007). A new S-box structure named affine-power-affine. International Journal of Innovative Computing, Information and Control, 3(3), 751-759.
Hussain, I., Shah, T., Mahmood, H., & Gondal, M. A. (2013). A projective general linear group based algorithm for the construction of substitution box for block ciphers. Neural Computing and Applications, 22(6), 1085-1093.
Zhang, X., Mao, Y., & Zhao, Z. (2014). An efficient chaotic image encryption based on alternate circular S-boxes. Nonlinear Dynamics, 78(1), 359-369.
Hussain, I., Shah, T., & Mahmood, H. (2010). A new algorithm to construct secure keys for AES. International Journal of Contemporary Mathematical Sciences, 5(26), 1263-1270.
Liu, H., Kadir, A., & Gong, P. (2015). A fast color image encryption scheme using one-time S-Boxes based on complex chaotic system and random noise. Optics Communications, 338, 340-347.
Ali, R., Ali, J., Ping, P., & Jamil, M. K. (2024). A novel S-box generator using Frobenius automorphism and its applications in image encryption. Nonlinear Dynamics, 112(21), 19463-19486.
Jamal, S. S., Ali, R., Jamil, M. K., Nooh, S. A., & Alblehai, F. (2025). Secure S-box construction with 1D chaotic maps and finite field theory for block cipher encryption. Alexandria Engineering Journal, 125, 278-296.
Garipcan, A. M., Aydın, Y., & Özkaynak, F. (2025). A novel S-box generation method based on metastable inducing over FPGA for block ciphers. Knowledge-Based Systems, 310, 112968.
Li, X., & Liu, H. (2025). Constructing Keyed Strong S-Boxes with High Nonlinearity Based on a 2D-Hyperchaotic Map and Elliptic Curve. International Journal of Bifurcation and Chaos, 35(08), 2550096.
Alali, A. S., Ali, R., Jamil, M. K., Ali, J., & Gulraiz. (2025). Secure medical image encryption with hyperelliptic curve based S-boxes. Scientific Reports, 15(1), 18179.
Hazzazi, M. M., Azam, F. E., Ali, R., Jamil, M. K., Nooh, S. A., Alblehai, F., & Arabia, S. (2025). Batch generated strongly nonlinear S-Boxes using enhanced quadratic maps. Aims Mathematics, 10(3), 5671-5695.
Aydın, Y., Garipcan, A. M., & Özkaynak, F. (2025). A novel post-processing approach for improving minimum nonlinearity in S-boxes: A case study based on 2D hyper chaotic Schaffer transformation map. Expert Systems With Applications, 128067.
Pieprzyk, J., & Finkelstein, G. (1988). Towards effective nonlinear cryptosystem design. IEE Proceedings E-Computers and Digital Techniques, 135(6), 325-335.
Weister, A. F., & Tavares, S. E. (1986). On the design of S-boxes, advances in cryptology. In Proceedings of CRYPTO’85, Springer, Berlin, Germany, 1986.
Biham, E., & Shamir, A. (1991). Differential cryptanalysis of DES-like cryptosystems. Journal of Cryptology, 4(1), 3-72.
Razaq, A., Yousaf, A., Shuaib, U., Siddiqui, N., Ullah, A., & Waheed, A. (2017). A novel construction of substitution box involving coset diagram and a bijective map. Security and Communication Networks, 2017(1), 5101934.
Hussain, I., Shah, T., Mahmood, H., & Gondal, M. A. (2013). A projective general linear group based algorithm for the construction of substitution box for block ciphers. Neural Computing and Applications, 22(6), 1085-1093.
Hussain, I., Shah, T., Gondal, M. A., Khan, W. A., & Mahmood, H. (2013). A group theoretic approach to construct cryptographically strong substitution boxes. Neural Computing and Applications, 23(1), 97-104.
Martinez-Diaz, I., Ali, R., & Jamil, M. K. (2025). On the search for supersingular elliptic curves and their applications. Mathematics, 13(2), 2227-7390.
Elkandoz, M. T., & Alexan, W. (2022). Image encryption based on a combination of multiple chaotic maps. Multimedia Tools and Applications, 81(18), 25497-25518.